Authenticating transactions or login sessions through SMS-based two-factor authentication is standard practice. However, SMS as a 2FA medium might not be totally secure. Hackers can intercept these messages and use them to log in to your account.
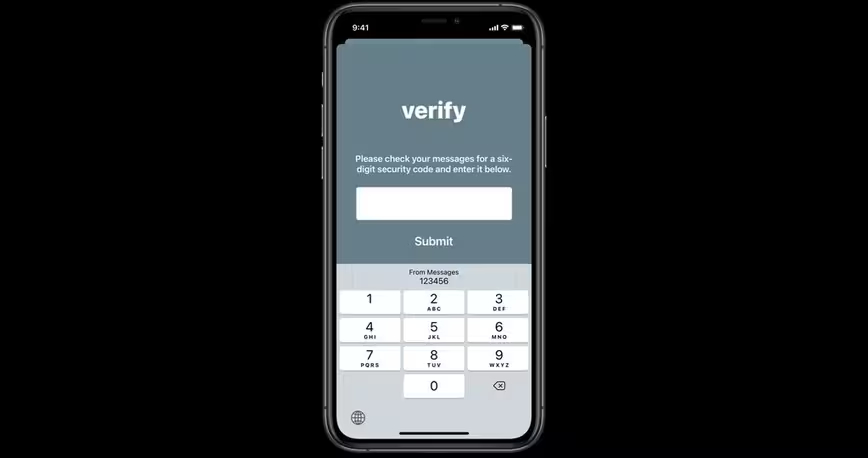
Apple is trying to make this method a tad bit more secure through domain-bound messages for developers. Make no mistake, the company’s new effort is trying to improve autofill — a function that lets you automatically put received code in the field.
Here’s how it works: developers will need to implement this functionality in their apps and websites. Once they do that, your autofill will only get code if it finds that the SMS delivered to your phone has the same domain as the app or website you’re authenticating.
Here’s Apple’s explanation:
For example, if you receive an SMS message that ends with
@example.com #123456, AutoFill will offer to fill that code when they interact with example.com, any of its subdomains, or an app associated with example.com. If instead, you receive an SMS message that ends with@example.net #123456, AutoFill will not offer the code on example.com or in example.com’s associated app.
Even if developers implement this, there might be a chance that sophisticated hackers can intercept your message and relay it back to you with meticulous details. Domain-bound messages might just make their task a bit harder.
If possible, you should use a software-based 2FA such as Authy or Google Authenticator
You can learn more about domain-bound codes here.
Get the TNW newsletter
Get the most important tech news in your inbox each week.