
Threat actors have exploited “obscure” bugs in WebKit and Chrome browsers to serve over 1 billion malicious ads in less than two months, a new research has found.
The attackers targeted iOS and macOS users with zero-day vulnerabilities in Chrome and Safari browsers that bypassed built-in security protections to show potential victims intrusive pop-up ads, and redirect users to malicious sites.
Cybersecurity firm Confiant has been extensively tracking the group — dubbed “eGobbler” — a name inspired by the Thanksgiving holiday, when researchers spotted their malvertising campaigns for the first time last year.
It’s worth noting here that the open-source WebKit browser rendering engine is the basis for Safari, in addition to the browsers bundled with Amazon Kindle ebook reader and Samsung Tizen OS.
Blink — the rendering engine that powers Google Chrome — is also a fork of WebKit. But on iOS, Chrome and other third-party browsers rely on WebKit due to restrictions imposed by Apple’s App Store Review Guidelines (Section 2.5.6).
This is far from the first time eGobbler has run amok with malicious ads. Back in April, the group exploited a Chrome for iOS exploit (CVE-2019–5840) to circumvent the browser‘s built-in pop-up blocker to deliver fake ads to 500 million sessions of users from the US and Europe in under a week.
The flaw was eventually patched after Google released a Chrome 75 update in June. But now, it appears eGobbler is going after a separate WebKit vulnerability in JavaScript to generate successful redirects.
Confiant said the new exploit (CVE-2019-8771) — now fixed by Apple in iOS 13 and Safari 13.0.1 after the bug was private disclosed to the company on August 7 — leveraged the “onkeydown” event, a JavaScript function that’s executed every time a user presses a key on the keyboard, to bombard users with pop-ups when users interact with a site by pressing a key.
What makes the JavaScript exploit more insidious is that it also impacts desktop browsers, thereby giving eGobbler an opportunity to expand their operations beyond mobile devices.
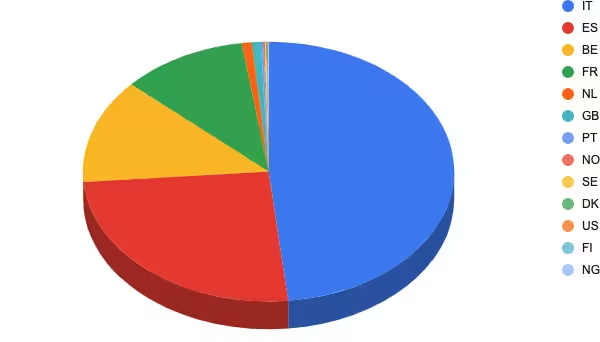
Between August 1 and September 23, the group served a staggering 1.16 billion malware-ridden ads, with European countries like Italy and France becoming the prime targets.
As always, the best way to protect against such adware campaigns is to be vigilant of your browsing activity and follow security best practices, which include keeping devices up to date with the latest software patches and restricting app downloads to only trusted developers on official app marketplaces.
Get the TNW newsletter
Get the most important tech news in your inbox each week.



