Cybersecurity researchers have detailed a dangerous botnet specifically targeting businesses to steal sensitive data and cryptocurrency.
Dubbed “MasterMana Botnet,” the ongoing campaign is believed to be connected to the “Gorgon Group,” a crew of cyberbaddies linked to worldwide criminal activity and repeated attacks on governments.
“This operation, which began as early as December of 2018, appears financially motivated, given the seemingly indiscriminate targeting of business email addresses via phishing and the inclusion of specific functions to steal information associated with cryptocurrency wallets,” said security firm Prevailion.
“While most companies fear they may become compromised by advanced actors, this particular report highlights that actors do not have to rely on advanced tools or techniques to have a serious business impact,” added the firm, which estimates that roughly 3,300 machines have been infected so far.
RATs are MasterMana BotNet’s best friend
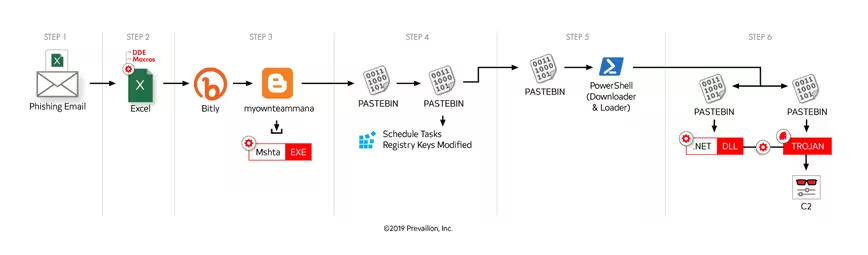
The campaign operates like this: victims are tricked into opening a phishing email that forces their machine to download a malicious .NET “dll” file. This file assumes system processes before installing a trojan that operates as a backdoor (particularly Revenge Rat or an Azorult variant).
Revenge Rat is a well-known trojan that allows a machine to be remotely accessed, while the Azorult variant analyzed by Prevailion was designed to steal usernames, passwords, web history, cookies, as well as contents of cryptocurrency wallets.
The Azorult variant is even reportedly capable of uploading and downloading files, and even taking screenshots of the victim’s machine. Analysts noted this could lead to the deployment of additional payloads such as cryptocurrency miners and ransomware.
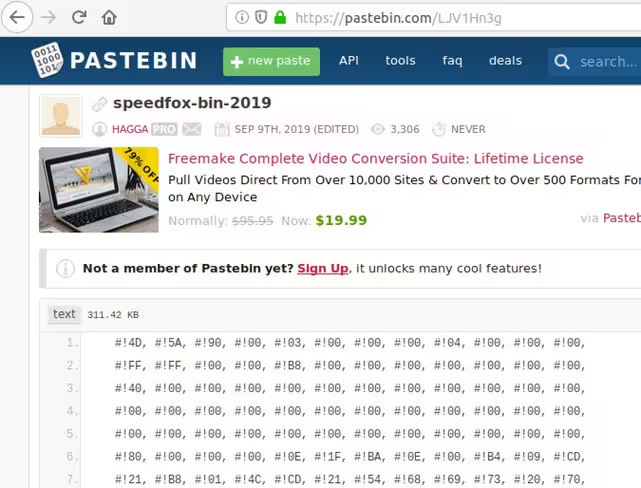
MasterMana Botnet is also noteworthy for the way it evades detection by pulling malicious code hosted by third-party websites such as Blogspot, Bitly, and Pastebin, rather than remote domains controlled by the attackers.
Prevailion also highlighted just how cheap the campaign is to run, as it leverages well-known trojans sold on dark web forums for $100. The only other reported costs were those associated with leasing Virtual Private Servers, which total around $60.
The firm warns that this particular threat actor is likely to continue operating the campaign. “[P]revious public reporting has not deterred them, therefore we wanted to highlight their new modus operandi, so that network defenders may more easily identify their operations.”
Get the TNW newsletter
Get the most important tech news in your inbox each week.