Cybersecurity researchers have identified a new strain of Linux malware that not only mines cryptocurrency illicitly, but provides the attackers with universal access to an infected system via a “secret master password.”
TrendMicro’s latest blog also reveals that Skidmap attempts to mask its cryptocurrency mining by faking network traffic and CPU-related statistics.
High CPU usage is considered the primary red flag of illicit cryptocurrency mining, which makes this functionality particularly dangerous.
According to TrendMicro’s researchers, Skidmap demonstrates the “increasing complexity” of recent cryptocurrency-mining threats.
Cryptocurrency mining malware is still a very real threat
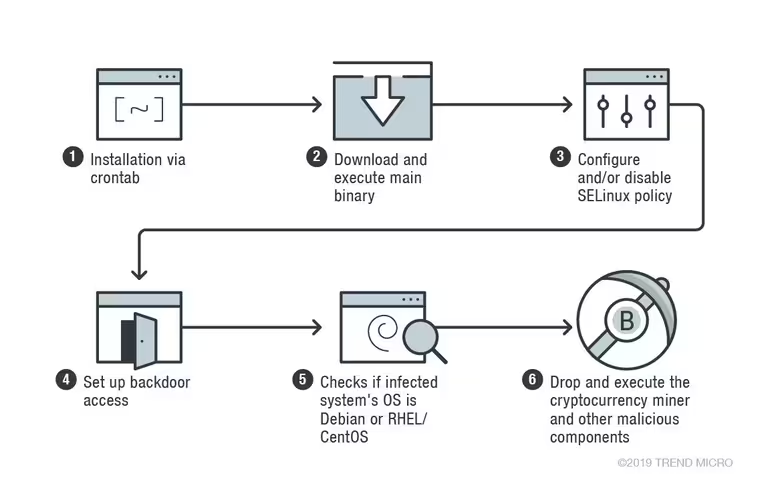
Initial infection occurs in a Linux process called crontab, a standard process that periodically schedules timed jobs in Unix-like systems.
Skidmap then installs multiple malicious binaries, the first minimizing the infected machine’s security settings so that it can begin mining cryptocurrency unhindered.
“Besides the backdoor access, Skidmap also creates another way for its operators to gain access to the machine,” wrote TrendMicro. “The malware replaces the system’s pam_unix.so file (the module responsible for standard Unix authentication) with its own malicious version […].”
“[T]his malicious pam_unix.so file accepts a specific password for any users, thus allowing the attackers to log in as any user in the machine,” added the firm.
Additional binaries are dropped into the system to monitor the cryptocurrency miners as they work to generate digital money for the attackers.
Unfortunately, TrendMicro didn’t indicate which cryptocurrency Skidmap illicitly mines. Hard Fork has reached out to the researchers for more information and will update this piece should they reply.
The firm warned that Skidmap is more difficult to cure compared to other malware, particularly as it uses Linux Kernal Module (LKM) rootkits, which overwrite or modify parts of the OS kernel.
Skidmap is also reportedly programmed to reinfect systems that have been cleaned or restored.
“Cryptocurrency-mining threats don’t just affect a server or workstation’s performance — they could also translate to higher expenses and even disrupt businesses especially if they are used to run mission-critical operations,” wrote TrendMicro.
To protect against Skidmap, TrendMicro urges admins to keep their systems and servers patched and updated, and beware of unverified, third-party repositories.
They should also enforce the “principle of least privilege” to prevent malicious binaries from obtaining access to critical system processes in the the first place.
Update 10:38 UTC, September 17: A TrendMicro spokesperson has since contacted Hard Fork to confirm that Skidmap mines Monero, the private-focused altcoin.
“The cryptocurrency miner pertaining to this article is a variant of XMRig which mines Monero cryptocurrency,” they said via email.
XMRig is open-source cryptocurrency mining software available on GitHub.
Get the TNW newsletter
Get the most important tech news in your inbox each week.