In a move to counteract the spread of browser malware, yesterday Google announced its plans to ramp up its security mechanisms in Chrome to make it easier for users to prevent and recover from unwanted software infections.
But good intentions aside, there is one aspect of this implementation that creeps me out: the same measures put in place to protect us are also enabling Google to scan precisely what extensions we download to our browsers and how we use them.
The push towards increased antivirus defenses comes only a week after reports broke out that a malicious adblock extension on the Chrome Store had been downloaded well over 37,000 times. The more pressing issue, though, was that there were hundreds of other infectious instances of the same app still in the wild.
This is precisely what the new security additions were designed to negate. But this is not to say that these measures come without any caveats.
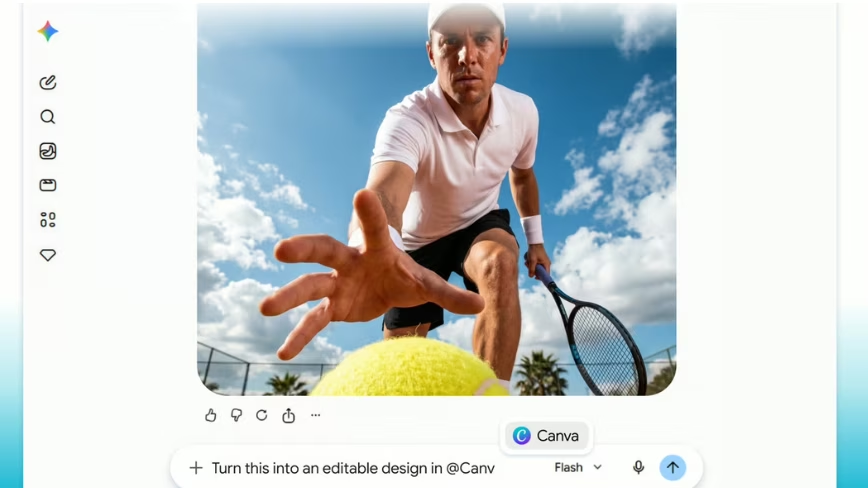
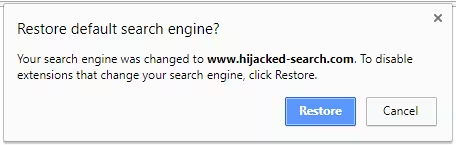
The first new feature makes it more difficult for extensions to make changes to your browser settings. To thwart such apps from tampering with your Chrome setup, the browser will now actively seek to detect when extensions have made changes without your consent and offer to revert all alterations with one click.
The second security addition builds on the already-existent Chrome Cleanup feature, which makes it easier to remove bundled software that third-party extensions have installed to your system without your knowledge.
The redesigned Cleanup functionality makes this process simpler and quicker.
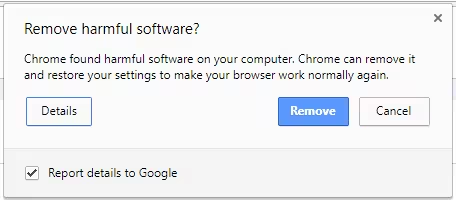
This leads us to the last and most troubling security feature – namely, the upgraded Cleanup engine.
Google collaborated with security firm ESET (whose Mac antivirus software was recently discovered to be susceptible to attacks) to upgrade Chrome’s sandbox technology with ESET’s detection algorithm which was designed to scour for violations and remove offending software.
As some users have pointed out, the upgraded Cleanup engine essentially works like Microsoft’s anti-malware SmartScreen filters in Windows 10. Unlike Microsoft though, it remains unclear whether Google will give Chrome users to opt out from this setting.
But here is the main issue: in order to perform this detection analysis properly, Chrome will be scanning through every piece of software you have downloaded and actively recording this data.
So why should we be worried about all this data Google collects? In a recent talk at Amsterdam-based tech hub TQ (disclaimer: TNW founded TQ), Alphabet executive chairman and former Google CEO Eric Schmidt was vocal the search engine heavyweight is comfortable to make most of its money from advertising.
“We are in the advertising business and we love advertising,” Shmidt said.
But while the Big G is happy to keep stacking capital from its ad streams, we ought to maintain a healthy dose of skepticism when we consider what implications this business model has for us, the users.
You know what they say: “If you’re not the customer, you’re the product.”
Whether or not it bothers you on a personal level, Google makes its money from studying our desires and attending to them more effectively – or empowering other companies to do so.
Yes, Google still cares about improving its line of services, but there is an added incentive to monitoring and analyzing how we use these products: what we do, how we do it, why we like doing it and what keeps us coming back for more is the fuel the Mountain View company needs to keep growing – and its aggressive scaling approach necessitates large quantities of that.
In a way, this is also what the new security features bring to Chrome: better functionality for the users and more gleanable insights for the maker.
Of course, Google wants to direct your attention exclusively towards what benefits you – not them. After all, its success depends on your docile acceptance that functionality matters more to you than privacy.
Get the TNW newsletter
Get the most important tech news in your inbox each week.