Android has a problem. New research shows that the mobile operating system’s encryption can be bypassed using a fairly straightforward brute force method.
The hack
Brute force is actually pretty simple; heck, you may have even done it yourself and not known about it.
All it really means is that you try repeatedly to enter the correct password (you know, like when you forget a password to an online account and just keep trying). Though Android uses a strong 2048-bit RSA key in addition to your password, devices using a Qualcomm processor (read: most modern Android devices) are at risk.
So how did the person who found the exploit, Gal Beniamini, get through that encryption? From Neowin:
That strong RSA key makes brute-force attacks, where a computer simply tries every single possible combination of a password, almost impossible.
However, the researcher proved that thanks to flaws in the way Qualcomm implements some security measures, combined with Android kernel flaws, an attacker could get that key. That means that all that stands between him and your data is your password. And we know how good users are at choosing secure passwords.

Qualcomm and Google
The good news is that the person who found the flaw is working with Qualcomm and Google on a fix. For its part, Google notes it has already paid Beniamini via its Vulnerability Rewards Program’ and patched its own issues.
Qualcomm is taking a less straighfroward approach. In a statement to Engadget, it pushes responsibility off onto partners:
The two security vulnerabilities (CVE-2015-6639 and CVE-2016-2431) discussed in Beniamini’s June 30 blog post were also discovered internally and patches were made available to our customers and partners. We have and will continue to work with Google and the Android ecosystem to help address security vulnerabilities and to recommend improvements to the Android ecosystem to enhance security overall.
Should you be worried?
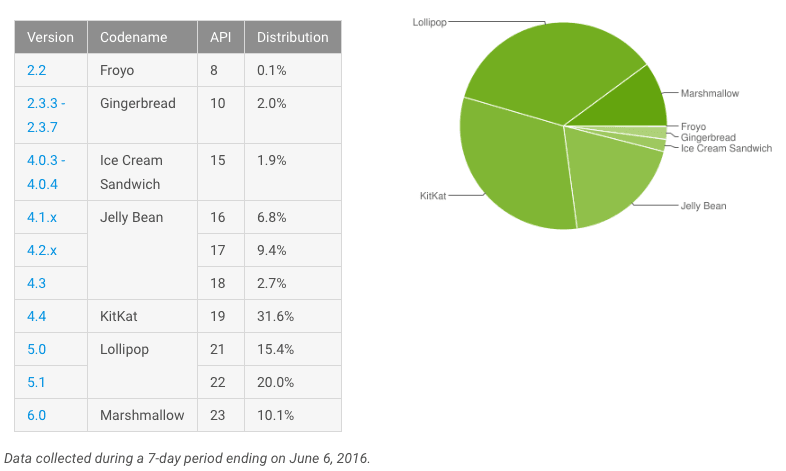
The exploit affects full-disk encryption, something used as a default on Android 5.0 and later. According to Google, about 45 percent of its users are subject to this exploit.
While some of the flaws can be patched, Beniamini notes that complete security “might require hardware changes” as some exploits can’t be fixed. The nature of the exploit also lends itself to off-device hacks, so a would-be thief doesn’t necessarily need to have your device in-hand.
It does take dedicated effort and know-how to crack into your device, and that’s not something a lot of people can do. This is a troubling look at Full Disk Encryption (FDE), something Google was very proud of at launch.
You probably don’t need to panic about whether or not anyone is stealing your information, but if you’re hanging your hat on FDE as a means to protect your device, this exploit shows why that may not be your best bet.
Get the TNW newsletter
Get the most important tech news in your inbox each week.