What do the Gallic Wars and online shopping have in common? The answer, believe it or not, is cryptography. Cryptography is the cement of the digital world, but it also has a long history that predates the digital era.
Most people do not realize that cryptography is a foundational element to our modern society. At it’s heart cryptography is about access to data, and controlling who can see and use it.
It is not only a vital part of everyday technology such as smartphones, but it is also enabling some of the hottest innovations like blockchain and the cloud — and therefore shaping our world as we know it.
So, let’s give cryptography the credit it deserves and take the time to understand how it all works — at least the basics!
An extremely brief history: From the Gallic Wars to World War II
Cryptography has been around for thousands of years. One of the earliest recorded uses of cryptography was (allegedly) by Julius Caesar. He used the Caesar Cipher about 2,000 years ago to send encrypted military messages.
The cipher was a substitution cipher in which each letter in the original message is replaced with a letter corresponding to a certain number of letters shifted up or down the alphabet. Only those with the key — which in this case is the number by which the alphabet is shifted — could decode the message. For example, if the key is three, then A=D, B=E, C=F, and so on.
The evolution of cryptography was gradual, but grand. It started with simple substitution ciphers, like Caesar’s, or permutation ciphers (one where you simply reorder the lettering, such as “hello” becoming “lehlo”). But as time went on and cryptography became more widely used and understood, ciphers naturally became more complex. Fast forward to today, where cryptography is a robust field with many industrial players, modern applications, and tools.
Most people have heard of the famous enigma machines that were used in the early to mid-20th century to protect diplomatic and military communication, most notably used by the Germans in World War II.
Enigma machines used substitutions defined by wirings of wheels of 26 characters. Each letter was encrypted by a different substitution because the wheels were always turning. This is why the enigma machine was so difficult to break.
The major crypto development that changed the world
In the mid-1970s there was a major development in cryptography that changed everything: public key cryptography. Before this development, it used to be that if Bob encrypted a message to Alice, the key he used to protect that message was the same key that Alice would use to decrypt the message. This is called a symmetric key algorithm.
Public key cryptography, however, uses an asymmetric key algorithm. In these systems Bob could use a public key to encrypt a message to Alice, but Alice would use a different private key to decrypt it.
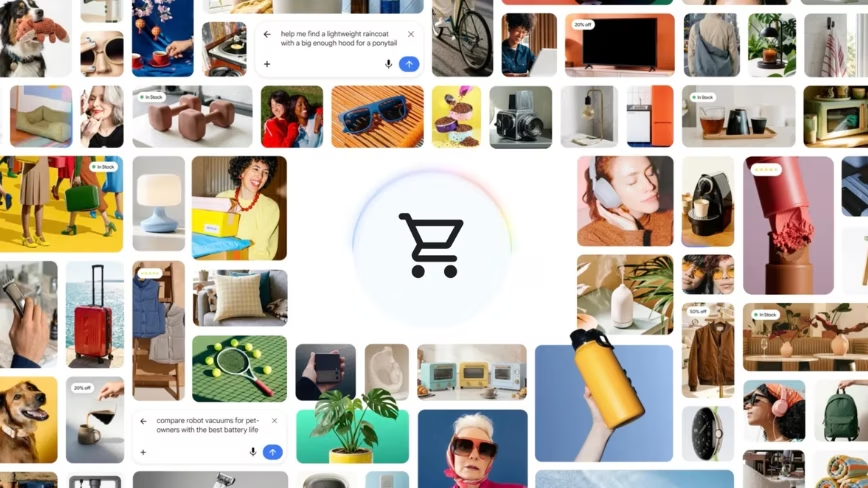
This adds a new layer of security as only Alice can decrypt the message since she is the only one with the private key. This is what makes online shopping possible. Credit card details are encrypted using a public key, then only the retailer has the private key to decrypt those details to finalize the transaction.
Blockchain and cloud computing, cryptography’s next frontier
Enabling ecommerce is only one of cryptography’s many major contributions to our digital world. As cryptography continues to evolve, researchers and technologists continually find new ways to implement it as we see the emergence of new technologies. Let’s take blockchain for example.
Just about everyone has heard of blockchain at this point, but not everyone understands it. To summarize, blockchain is essentially a shared database populated. Blockchain technology provides a secure, efficient way to create a tamper-proof log of activity. The most widely known application of blockchain is for Bitcoin and other cryptocurrencies.
Cryptography is used in two ways here. The first is via algorithms called cryptographic hash functions.
Using a chain of hashes of the database ensures that the order of transactions is preserved. Thus, the blockchain creates a something akin to what in finance is called a ledger. But unlike a centralized ledger held at one bank, a blockchain ledger is distributed across many computers, with each computer having the same view of the ledger. This is why one often sees blockchains referred to as “distributed ledgers.”
Hash functions are also used, in the Bitcoin protocol, to ensure that everyone’s view of the ledger is the same. This is done by a process called “mining.” The Bitcoin miners search for hash values which satisfy a certain property, as they expend effort (energy) doing this for successive hash values, the effort of reversing the ledger and changing it becomes prohibitive.
This is a very inefficient method (in terms of energy consumption) of ensuring everyone’s view is the same, and other types of blockchains take different approaches to solve this problem so as to use up less of the earths energy resources.
The second way cryptography is used in this instance is to create digital signatures, which are used to provide authentication, data integrity, and non-repudiation. A digital signature is generated by combining a user’s private key with the data he or she wishes to sign. Once the data is signed, the corresponding public key can be used to verify that the signature is valid.
These digital signatures are used to ensure the data put on the blockchain is valid. In Bitcoin the digital signatures are used to ensure the correct amount of value is transferred from one Bitcoin wallet to another. For example, the digital signature ensures that Alice transferred the value out of her Bitcoin wallet, and not out of Bob’s wallet.
I know this may all sound complicated, but the final point is this: blockchain and cryptocurrency would not be possible without cryptography.
Our heads in the clouds
Another technology that couldn’t evolve into what it is without cryptography is the cloud. The cloud could exist without cryptography, but not in a secure fashion. As we have seen over the past several years, cloud computing offers a massive range of benefits for companies, but there is a slew of new security issues including logging in, keeping credentials secure, protecting data in the cloud — the list goes on. This is where cryptography comes into play.
Cryptography makes sure that the credentials and data stored in the cloud are encrypted, so that no one can get them without the key. Even if someone is able to get a hold of your credentials, if data is properly encrypted, a cybercriminal won’t be able to access your data without the key. Therefore, it’s also very important to protect the key itself.
As more data needs to be encrypted in the cloud, there are new technologies being developed to ensure that this is efficient and sustainable in the long term. For example, encrypted search has become an important development, as this allows you to search data on the cloud, while keeping it encrypted.
Without this, it would be virtually impossible to mine through all your data stored in the cloud without exposing it all and putting it at risk, unless the data was held in an unencrypted form; which would produce security risks.
Another emerging technology improving cloud security is multi-party computation (MPC), which provides a way for two or more parties to jointly compute a function over their inputs while keeping the inputs private.
The way this works is if two parties want to compute a function over data X, then one party holds some data (say Y) and the other party holds some other data (say Z), such that if you know Y and Z you can recover X, but if you only know Y then you know nothing about X.
This is a form of encryption, one can think of Y as the key and Z as the ciphertext (or vice-versa). Then, using this special form of encryption the two parties can compute a function on all of X, without revealing to the other party the value that they hold. Thus, MPC allows one to compute on encrypted data, if the data has been encrypted by this form of “encryption,” which is commonly called secret-sharing.
As cloud adoption continues to rise, it’s important that everyone continues to adopt these technologies quickly. As technology advances, we will see the deployment of more complex cryptography concepts in cloud environments.
The possibilities are infinite
Future applications of cryptography are boundless, especially when you consider what’s possible with MPC. Think about what could be done if you combined machine learning and MPC in the medical field. People who want advanced genomics could use MPC to process data and do experiments, without ever compromising privacy. And that’s just one of many possible scenarios!
Our world is advancing faster than ever before and it’s easy to lose sight of the foundational elements of technology that enable us to live our lives the way we do. Cryptography went from being a technique used to communicate with the military to being one of the cornerstones of the modern world.
As technology touches every single person’s life today, I believe it’s important for everyone to understand the basic concepts that allow technology to operate, and appreciate that cryptography has the potential to propel us to new heights not even yet imagined.
Get the TNW newsletter
Get the most important tech news in your inbox each week.