
Time and again, we hear of incidents involving identity theft, stealing of account passwords, installation of malware from web sources, and even ransomware.
All of these security breaches have a certain attack vector in common, and that is social engineering – when you’re tricked into clicking on a link you’re not supposed to, and when you open files or applications from dubious sources. It’s an easy mistake to make, especially when the website looks legitimate, but it’s also easy to avoid — if you know what SSL is.
If you think about it, you’ll probably recall that there’s a green padlock icon on your online banking website, and it usually includes the name of your bank. That’s SSL and it’s what will save you from becoming a victim of nefarious hacks.
![]() In this article, I will explain, in layman’s terms, what SSL means, and its importance in today’s everyday computing.
In this article, I will explain, in layman’s terms, what SSL means, and its importance in today’s everyday computing.
What is SSL, and how does it work?
Let’s start with the basics: SSL stands for Secure Sockets Layer.
SSL is the standard implementation for establishing a secure and encrypted link between two points on the internet — say your computer and a web server.
It has since been updated to SSL/TLS or Secure Sockets Layer/Transport Layer Security, but it is still known simply as SSL for simplicity. It is also the basis for secure HTTP or HTTPS — it is basically a website transported through hypertext transfer protocol that goes through a secure, encrypted connection.
Too much jargon? Let’s simplify it even further, with some analogies.
Suppose you want to open an account with your local bank. You approach the teller, but she does not want to open one for you, since she does not know you (and since your account will be the basis for future transactions). One option is for the bank to call the authorities (the state department for example, or social security, or the department of motor vehicles) since they have your identification.
But that seems to be tedious, so she asks for identification, instead. You provide your passport, which contains your personal details, biometrics, etc. This serves as the document that authenticates your identity. However, the document in itself does nothing exceptional except identify you. You cannot use it to withdraw money from your bank, per se.
However, because your passport is an identifying document issued by a trusted authority (the government, the state department in particular), you can use it to open an account, acquire and ATM card, which you can then use to withdraw from the bank.
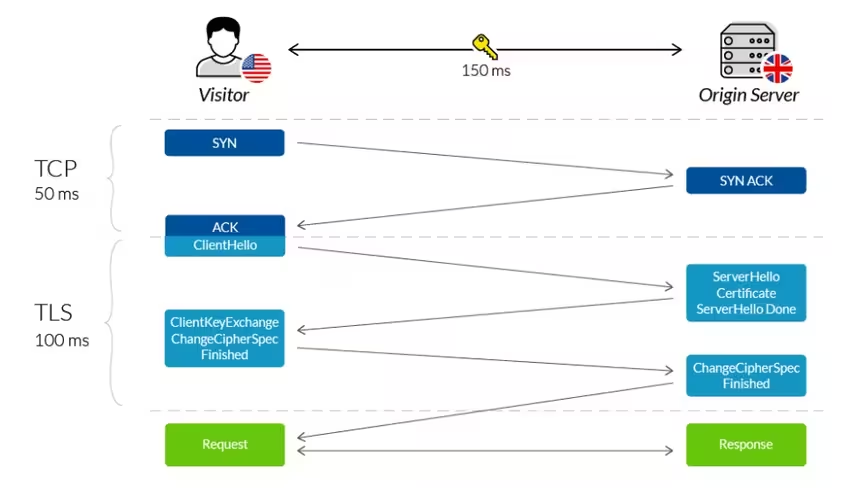
Similarly, the same scenario happens when you are accessing a secure website. Your client seeks authentication and identification from the web server, which it presents through its SSL certificate. The website cannot simply say “I am bank of America” — it needs a trusted certificate provider to establish this identity. This actually takes the form of an SSL handshake, which is a back-and-forth communication to establish a connection and identification before the web browser actually requests the needed information.
Is it that simple, then? Can’t I just acquire a certificate from a cheap provider?
Now, not all SSL certificates and certificate providers are made equal.
Some are enterprise-grade certificates and cost a pretty penny (worth thousands of dollars annually or so), while some are practically free, such as with LetsEncrypt.
An analogy here is that your passport is a secure indication of your citizenship to a country, and it is a trustworthy document that establishes your citizenship and identity. It can even be used to travel to other countries. Note, however, that not all passports are the same. Some are more “powerful” than others, since a bearer can travel to more countries without requiring a visa. For other passport bearers, they are required to secure additional documents (visa or other travel documents) before being granted access to a country.
In the same breath, SSL certificates are different. In the example above, for example, the certificate’s name itself is displayed on the browser, and it is one of the top-tier types of certificates. Most lower-grade certificates only indicate the “Secure” icon, but the certificate owner’s name is not presented.
![]() Granted, not all websites require the security of a bank website.
Granted, not all websites require the security of a bank website.
If you run a small blog, then security is appreciated, but not a deal-breaker. If you run an ecommerce website or a fintech company, however, users are bound to share details like addresses, card numbers, and the like. In this case, it would be necessary to have a top-tier SSL certificate.
SSL certificates come in different grades, as assessed by platforms like ssllabs.com. For example, The Next Web has an A+ certificate.
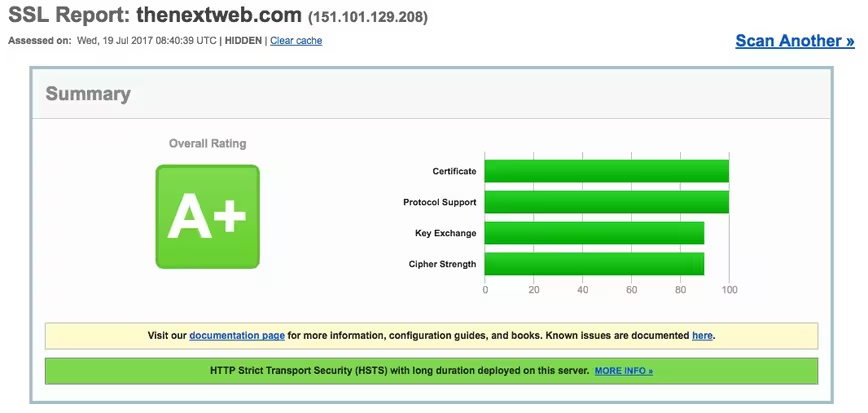 One way of establishing a Grade A+ certificate without spending a lot is by deploying your website or app infrastructure over a content delivery network that itself has a Grade A+ certificate, wherein your website will inherit the CDN’s own SSL certificate grade.
One way of establishing a Grade A+ certificate without spending a lot is by deploying your website or app infrastructure over a content delivery network that itself has a Grade A+ certificate, wherein your website will inherit the CDN’s own SSL certificate grade.
Let’s recap
This does not preclude other potential dangers, such as social engineering attacks, spoofing attacks, and other such attack vectors that can circumvent the security of connections.
To conclude with my earlier analogy, it’s like someone creating a fake ID and pretending to be you while making a transaction at the bank, or someone stealing your ATM or credit card and using it to buy items or withdraw money (with the right PIN).
Still, SSL is certainly the bare minimum of ensuring security of transactions and communications across client and server. No website or application should be without it, and you, as a user, should be wary of sending information across non-secure connections.
Get the TNW newsletter
Get the most important tech news in your inbox each week.




