Technology addiction has become rampant in recent times, thanks to the explosive evolvement of technological devices and the ease of use associated with it. Researchers define it as an uncontrollable urge to use different technological devices ranging from smart phones, social media, personal computers and gaming rigs.
It’s more prevalent among teenagers who shy away from social interaction in reality and find a peaceful abode in a welcoming technological world, where there’s a meager chance of social contact. All in all, it’s an easy way for them to fulfill their social needs without having to leave the comfort of their couch. According to researchers, technology abusers are more likely to have underlying health concerns such as depression and anxiety, and often possess impulsive behavior.
The Dark abyss of Smartphones
Let’s dig deep and take an example of smartphones. Gone are the days when the brick shaped mobile phones with features like inbuilt games, ringtone maker and sms were considered a technology straight from the heavens. But, with the unimaginable features they have to offer, smartphones have now become our digital companions (replacing humans) without whom we can’t paint our everyday life.
However, the picture is not as glittery as it seems. With the increased usage, security stakes have increased, with every other day plagued by the news of a new hack attempt on Smartphone users. The biggest threat to Smartphone users comes from the third-party apps. These apps are considered notorious for leaking personal information including usage trends, web history, personal pictures and chat-logs which is then used for numerous purposes including unwanted advertisements based on personal buying habits and even blackmailing by unscrupulous elements.
Furthermore, smartphones might also cause a disastrous data leak if you tend to engage in a lot of activity at the same time. It might happen if you “copy” something very important from your work related email in your clipboard and then subsequently post it unwittingly as a social media public post or in someone’s WhatsApp message. This scenario, if unfolds, might leak important information related to the company which may scarily end up in the hands of competitors or some hacker.
Even Twitter’s own CFO once posted a confidential message via a public Tweet, even though the message was intended to be sent as a Direct Message. These scenarios emanate from the fact that “majority of smartphone users have abandoned text messages in favor of messaging apps”.
The mother of all addictions, social media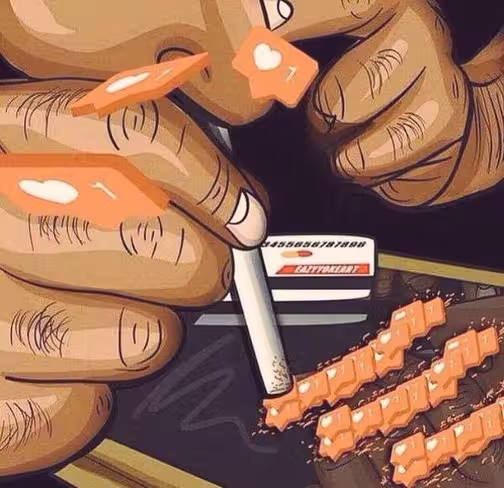
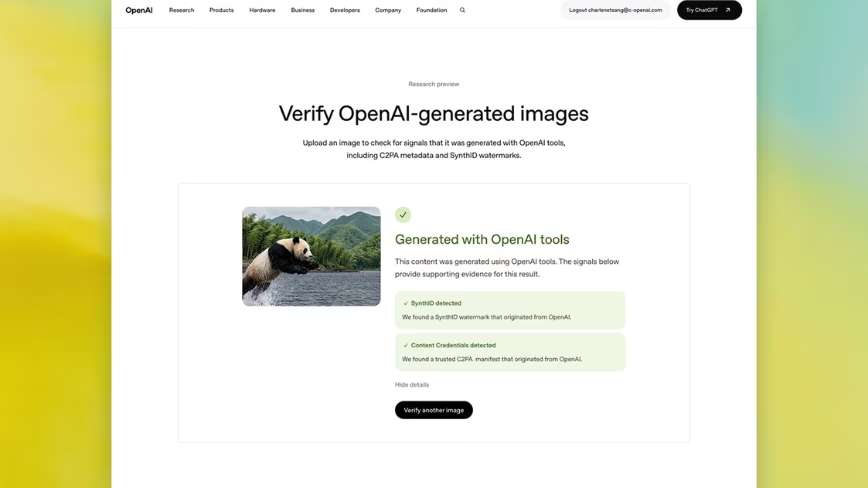
Similarly, social media addiction is attributed to social network companies and social content creators working hard to make their social media platforms irresistible with new features launched every other day. There’s a concept called FOMO — fear of missing out — associated with the addiction to social media and this involves urge to know everything that’s going on around us and to be a part of these happenings.
The main tool used by the social media giants like Facebook, Google+ and, Twitter is algorithmic filtering. This involves tweaking algorithms on daily basis and then monitoring the response of users to see if the tweak has increased their engagement. Now, how does it feel like being a lab rat in a giant, global experimental lab?
These experiments might prove profitable for social media companies but not us. Think of the last time where you posted a social media story from your home or office, or shared an important life event via Facebook or Twitter. Incredulously, a harmless or useless looking post might give enough information to an outsider which might come handy in wrecking havoc to your life. Similarly, employees have, over the time, used social media to connect their companies to the outside world. Be it an important company event, a job posting or a promotion.
But, little do they know that they are sharing too much information impulsively via a single post. A geeky cyber criminal might paint a complete picture of that employee through social media activities and may deliver a spear phishing email through the very same contact details provided to send in resumes for the job post by that employee. Count the odds if a hacker sends you an email titled “How you can save up $200 on a single flight” at the same time when you are planning for a vacation because he already knew your plans through the Facebook post you published only moments ago.
Interactive world of online gaming
The love of online gaming is deep rooted in our younger generations. Generation Z has the perks of interacting over their favorite games and talk to the people they don’t know at all. This comes with the increased risks, especially viruses, identity theft, and phishing attacks.
With the need of creating heavily decorated profiles on gaming platforms, it has become quite easy for hackers to gain access to your personal details and credit card information. The most worrying aspect is the use of parent’s credit cards by their kids which means hackers and cyber criminals have access to a large sum of money.
In addition, gamers might get hooked to social engineering scams where a completely unknown person sends them a friend request and trick them into sending vital information such as virtual goods, account details or credit card numbers.
What can be done to avoid this?
As simple as it sounds, the most important instrument we have to dodge tech espionage is our “brain” coupled with our greatest tool, “common sense”. While we tend to skim a lot of information over the internet but sometimes, it’s necessary to grasp a little more knowledge which might come handy.
Whatever you do with the use of technology, if you have the negative consequences in mind, you would think thrice before jumping into the bandwagon of sharing spree.
Get the TNW newsletter
Get the most important tech news in your inbox each week.