![Ask.com was leaking server logs and everyone could see what you searched [Update]](https://media.thenextweb.com/2017/04/Pasted-image-at-2017_04_07-03_30-PM-1.avif)
Update: Ask.com has since informed us it has resolved the issue globally. A spokesperson told TNW the following:
We have been working to address the inadvertent publishing of the Ask.com server status page and can report that this matter has now been globally resolved. We can confirm user IP addresses were not accessible during this incident, only queries and the IP addresses of our internal servers. We regret this error and are committed to protecting the confidentiality and security of our users’ information.
It seems Ask.com is suffering a massive technical issue which is causing it to reveal everything people are searching on its website.
The leaked search queries are being displayed on the company’s dedicated server status page for everyone to see.
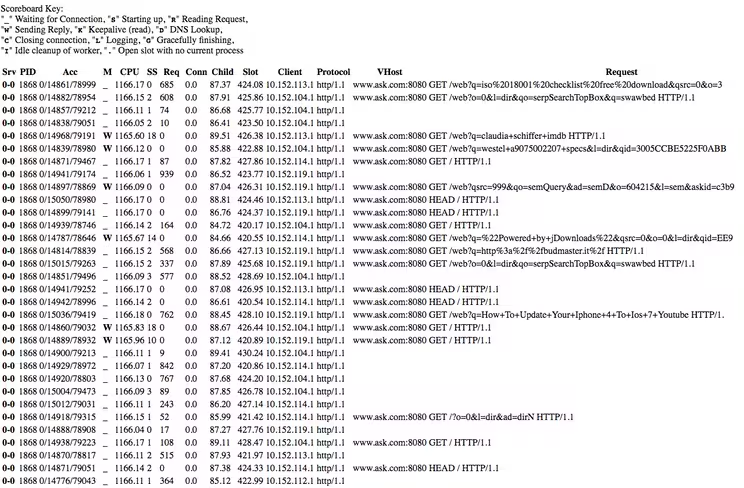
Here’s a screenshot of some of the leaked data:
It remains unclear what is causing the malfunction, but it appears the page is adding new entries anytime it is refreshed.
The issue was first spotted by Paul Shapiro who took to Twitter to notify users about the glitch.
Oh gosh! https://t.co/ArNClLQsly is leaking its server logs. Look at what people are searching: https://t.co/wy08gSrgwq
— Paul Shapiro (@fighto) April 7, 2017
While we’re not sure about the details, it is highly unlikely Ask.com opened the page to the public intentionally as server pages are traditionally kept private to help technicians effortlessly monitor unexpected errors.
It essentially works as a utility tool for tracking and troubleshooting issues experienced on the Apache server.
While the leaky server logs don’t directly pose a major security threat, it’s not common practice to leave out such details to the public eye.
According to security experts familiar with the matter, the good thing is that it appears Ask.com is not displaying the IP addresses of searchers – though the leak is still a worrisome fail.
We’re currently reaching out to Ask.com for further comment and will update this piece accordingly. Meanwhile, better think twice before using it – or risk having thousands of people browse through your search queries.
Update: We warned you – your nasty searches are really starting to pop up:
@fighto Just vomited on keyboard Paul. pic.twitter.com/hp1pa5ER28
— Tony Spencer (@notsleepy) April 7, 2017
Update 2: Upon closer examination, it seems the queries displayed at the server status page are HTTP requests, even though Ask.com uses HTTPS.
Update 3: We have been informed that the IP’s displayed on the status page were not the addresses of users, but rather those of Ask.com’s own servers. The reason this happens is because all requests are load balanced before they hit the website’s search system.
So while the leaked server logs do indeed show searches by real people, their IP addresses are all protected.
[H/T Paul Shapiro]
Get the TNW newsletter
Get the most important tech news in your inbox each week.





