Earlier this week, a CNBC columnist tried to drive home a point about the importance of strong passwords. In the piece, which has since been deleted but is available in cached form, CNBC included a rather lame excuse for a security tool that sought user’s passwords in order to test their strength.
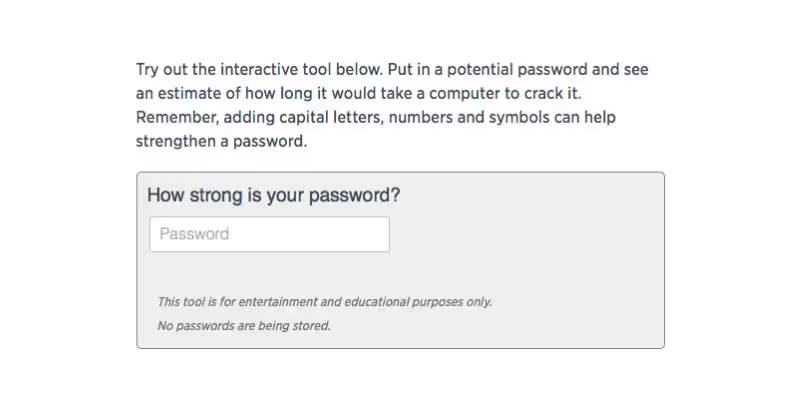
Weak passwords showed warnings as well as tips to improve password strength, such as adding additional non-alphanumeric characters, using non-dictionary words and adding length. Great advice.
After a user submitted their password the form reloaded with details about how strong a password is.
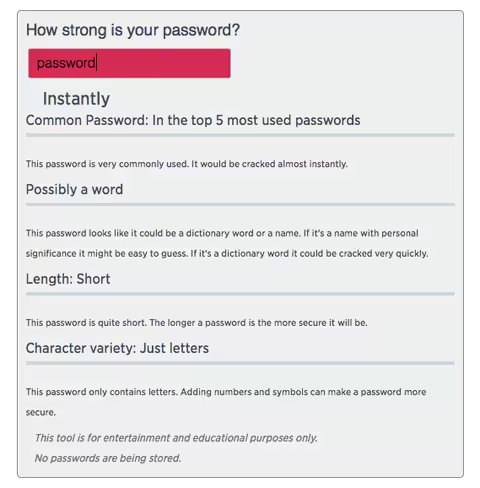
That’s where the problem lies: to submit a form with saved information the information has to be, well, saved. CNBC’s form saved this information over a non-secure HTTP connection which could conceivably provide hackers with access to plaintext (non-encrypted) passwords. It also added the string (your password) to the end of the reloaded URL.
In theory, a hacker sniffing a network for traffic could see these URLs — now with your password appended to the end of it — and wreak havoc.
The reality of the matter is, something like that is pretty unlikely. Even after finding a password you’d still have to match it up with additional information for it to be of any use (such as a username or an email address) two things the form didn’t ask for.
While it may not be a huge security threat for those that tested their actual passwords in the tool, it doesn’t make the exercise any less dumb on CNBC’s part.
And apparently, CNBC agrees — they’ve since removed the post and the password tool.
Just working on my new news app. pic.twitter.com/60Z3grWtB7
— Jeremy Bowers (@jeremybowers) March 29, 2016
To be on the safe side, it’s not a bad idea to change your password if you used the tool.
Get the TNW newsletter
Get the most important tech news in your inbox each week.




