
As if the spectre of being hacked while surfing the Web isn’t bad enough, there has been a surge in the number of attacks on people who misspell the names of popular websites.
In a study carried out by Endgame, the cyber security firm has found more than 300 well-known companies, such as Netflix, YouTube and Google had been targeted in an attempt to ensnare careless typers online.
The culprits have been registering domains such as googgle.com, googlw.com and Netflix.om – the latter points to sites registered in Oman – which have the look and feel of the site the searcher is looking for. However, these are loaded with malware and attempt to convince the browser to share their personal details.
The issue has existed for some time, but Endgame reports, there has been an upturn in the number of sites using the .om suffix – which would typically indicate that the site in question had launched operations in Oman. But a quick search turns up nothing.
Effects can be relatively mild, such as: the user is redirected to objectionable material; the user is presented items for purchase from storefronts of questionable repute; or the user sees content that unfavorably portrays the intended brand or site. Effects can also be much worse. The malicious actor can spoof a real site to harvest login credentials, place backdoors on a system, install ransomware, or really anything else of his choosing.
Below is a list of popular domains with a .om address.
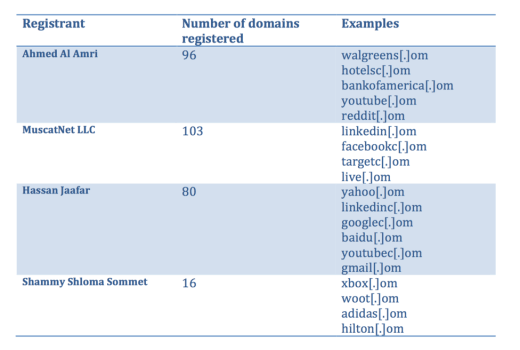
The research discovered that the vast majority of .om registered domains are malicious. Many popular sites remain unregistered here and therefore vulnerable, it concluded.
However, hackers aren’t immune to the occasional typo. This month a group in Sri Lanka were caught hacking into the servers of a Bangladeshi bank after they misspelt the word ‘foundation’.
➤ Don’t googel it: hackers target poor spelling [The Times]
Get the TNW newsletter
Get the most important tech news in your inbox each week.





