With a bit of ingenuity, and a $60 USB dongle available on Amazon, hackers can now access your computer with just 15 lines of code, from more than a hundred feet away.
The researcher who found the ‘MouseJack’ vulnerability, Marc Newlin, recently published a report detailing his findings.
MouseJack is a collection of security vulnerabilities affecting non-Bluetooth wireless mice and keyboards. Spanning seven vendors, these vulnerabilities enable an attacker to type arbitrary commands into a victim’s computer from up to 100 meters away using a $15 USB dongle [now $60].
Newlin’s research points to a flaw in the way several vendors configure their non-Bluetooth wireless mice and keyboards. These devices use a USB dongle to listen for radio frequency transmissions from either of the two input devices before executing the desired action.
Most vendors have encrypted these communications but those that don’t are vulnerable to attackers using a USB dongle that force-pairs a fake keyboard to the victim’s wireless dongle and allows it to send keypress packets conveying remote commands.
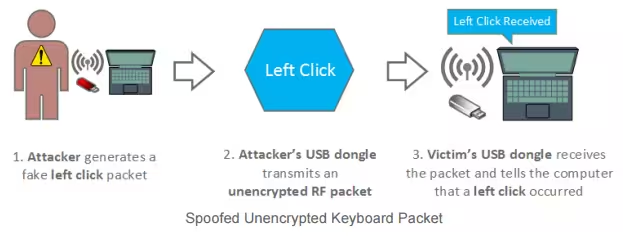
These same commands could them be used to install a rootkit or malware as if the attacker were sitting at the victim’s keyboard.
If you have one of the affected devices, you should download and install the patches as soon as they become available. Or, you could go old school and grab that wired mouse and keyboard that’s collecting dust in the closet.
Newlin plans to present his findings at next week’s RSA conference.
➤ MouseJack [Bastille Networks via Graham Cluley]
Get the TNW newsletter
Get the most important tech news in your inbox each week.





