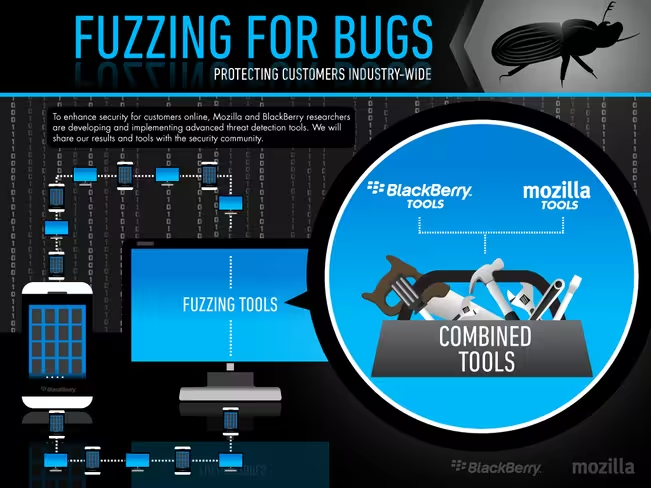
Mozilla today announced two developments in security on the Web. The first is a partnership with BlackBerry to collaborate on advanced automated security testing techniques called fault injection (commonly known as fuzzing) and the second is an open source security testing platform called Minion intended to be used by developers and security professionals.
For those who don’t know, fuzzing is a method of automated security testing used to proactively identify (and then fix) potential security flaws before they are leveraged against users. The technique usually consists of specially designed software to inject a variety of unexpected or malformed data into a specific application, program, or area of code to uncover where it is not being handled correctly.
Mozilla’s and BlackBerry’s joint research is focused on building out Peach, an open source fuzzing framework, for testing Web browsers. They will also be working on other fuzzing software, as well as fuzzing techniques and approaches to jointly raise the security protections for their combined users.
Both companies already used fuzzers extensively. Mozilla has successfully used Peach to perform fuzz testing against various HTML5 features (image formats, audio/video formats, fonts, multimedia APIs like WebGL and WebAudio and protocols used in WebRTC) and further secured Firefox and Firefox OS users. BlackBerry meanwhile has used large-scale automated testing to identify security issues in its products and services via third-party fuzzers and its own proprietary fuzzing tools, static analysis, and vulnerability research.
As for Minion, the platform has been under development by the Security Automation team at Mozilla for the past year. It aims to enable integration and adoption of automated security testing by allowing any team to set up the basic requirements to perform automated scanning and testing of websites and services with “sensible” defaults for plugins.
Minion has reached version 0.3, at which point Mozilla says several milestones have been achieved that allow it to be used internally across the company’s development community, quality assurance, and security teams. That being said, it is still under active development and “many new features are in progress.”
Mozilla says Minion focuses on correct and actionable results that don’t require a security professional to validate. While many security tools generate large amounts of data that often require a security professional to decipher, Mozilla’s platform is designed so every developer, regardless of security expertise, can use it to increase the security of their applications.
If you’re interested in Minion, you’ll want to check out the Github repository, development mailing list, and the official wiki. Most importantly, the platform’s roadmap is as follows:
- Site Ownership Verification: This is a critical feature that enables users to demonstrate ownership of a site before initiating scans.
- Granular Access Control: The ability to govern users ability to scan by group and site ownership as well as role.
- Improved Results Reporting: Now that there is working and reliable core platform, refinement of plugin results and improving reporting is a core objective.
- Deferred Execution Plugins: Sample implementations of invoking third party services so that Mozilla can demonstrate integrating with other Security as a Service platform.
- Reporting Plugins: Mozilla intends to implement a pluggable reporting interface, including the ability to add plugins to modify the risk ratings based on the security posture and priorities of the teams using Minion.
- Landing Pages: It may be desirable to generate metrics and dashboards, and to facilitate that Landing page support will be implemented to allow customization for user views.
- Cohort: A branch of Minion that will enable analysis of source code repositories and perform static analysis.
- Historical Issues: In order to facilitate ongoing tracking of a security program, support and integration for third party issue trackers (initial targets are Bugzilla and Github), and the ability to compare multiple scans over time will be implemented.
“These research efforts are some of the many ways Mozilla helps make the Web more secure and protect Firefox users,” Michael Coates, Mozilla’s Director of Security Assurance, said in a statement. Yet as the BlackBerry partnership shows, the dedication to improving security on the Web is commendable because it extends beyond just Mozilla’s own products.
Top Image Credit: Miguel Saavedra
Get the TNW newsletter
Get the most important tech news in your inbox each week.