Late last month, Rovio, the company behind Angry Birds, released a very popular game called Bad Pigges on Android (free), iOS ($0.99 to $2.99), and Mac ($4.99). Those who don’t have an Android device but still want to play for free are out of luck. Cybercriminals are capitalizing and have already created fake versions of the game, and put them on the Chrome Web Store. Please be aware: there is no free version of this game for the Web, nor for Google Chrome, and if you find one, chances are it will inject ads into your browser, whether you’re running Windows, Mac OS, or Linux.
Barracuda Labs did some digging and found that searching for “Bad Piggies” in the store gave back at least eight matches. If they don’t have it in the title, all these plugins have “Bad Piggies” in their game descriptions, so that they still show up when you search for the game.
The security firm’s investigation found that seven of the eight extensions it found come from the same source (playook.info), a maker of “free” flash games. I searched the store, and indeed came up with 7 fake games from the site, though out of a total of 11 results.
Furthermore, when you try to install any of them, they request permission to “access your data on all websites.” To play a game? Yep. If that doesn’t sound warning bells for you, I don’t know what does.
Unsurprisingly, the none of the games are authentic: they are not Bad Pigggies, but are simply just pigs-shoot-birds games. More importantly, after any of these “games” are installed, additional ads start to appear on various popular websites.
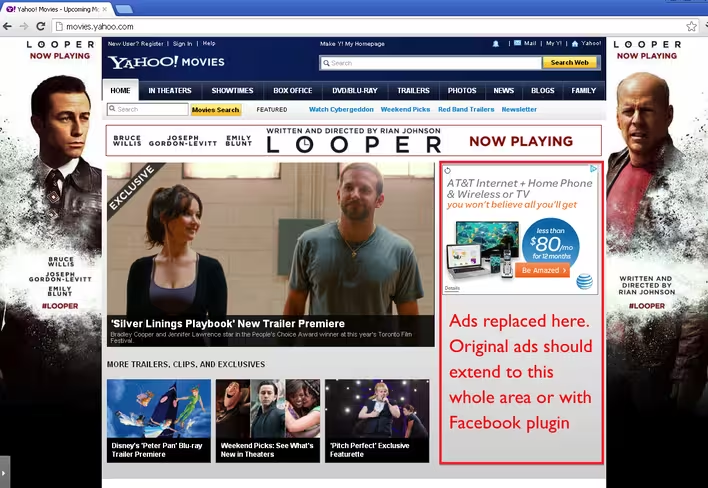
For example, here’s Yahoo, with extra ads:
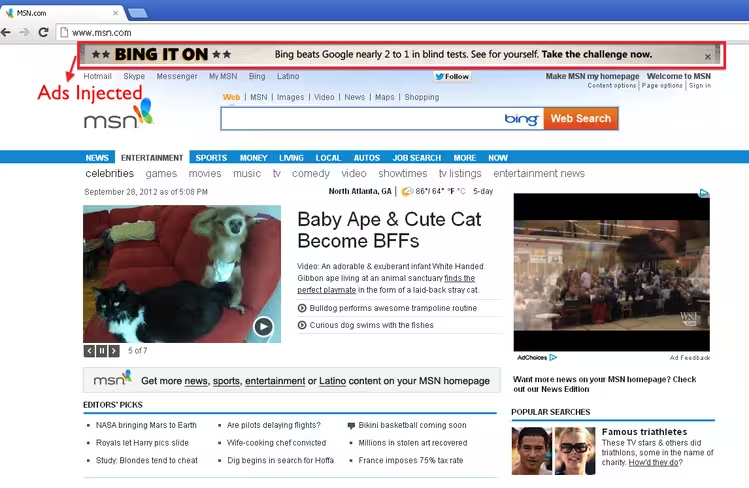
Here’s MSN, with extra ads:
Barracuda’s analysis shows that special code in one of the extensions checks to see if the page originates from certain Web sites and if so, inserts its own ads from playook.info. In fact, that particular extension has a list of 56 sites it watches for to inject ads into, including Angry Birds’ Chrome site, Disney, eBay, IMDB, Kickass Torrents , MSN, Myspace, The Pirate Bay, Yahoo, V9, 9Gag, and various other sites, particularly gaming portals.
The security firm has some advice to share:
A suggestion to Chrome users; whenever trying to install a plugin inside the Chrome web store, consider the requested permissions with a critical eye toward the intent of the plugin. If the plugin requests any permission that does not seem reasonable, do not install it. If you have already installed, uninstall them immediately and change your passwords on other websites if possible.
As Chrome gains more browser marketshare, Google should provide better secure solutions on Chrome web store to protect its users. Until then, it’s especially important that Chrome users know how to protect themselves.
Since these extensions are still in the Chrome Web Store, I have contacted Google about this issue. I will update you if and when I hear back.
Update at 9:50PM: “We’re working on getting the extensions removed now,” a Google spokesperson said in a statement.
Image credit: Marcus Beltman
Get the TNW newsletter
Get the most important tech news in your inbox each week.