When Google unveiled its latest mobile developments at the launch event for the Galaxy Nexus and Android 4.0 (codenamed Ice Cream Sandwich), fans of Google’s open-source mobile operating system were overjoyed to see a raft of new features, services and improvements included in the Google’s latest firmware release.
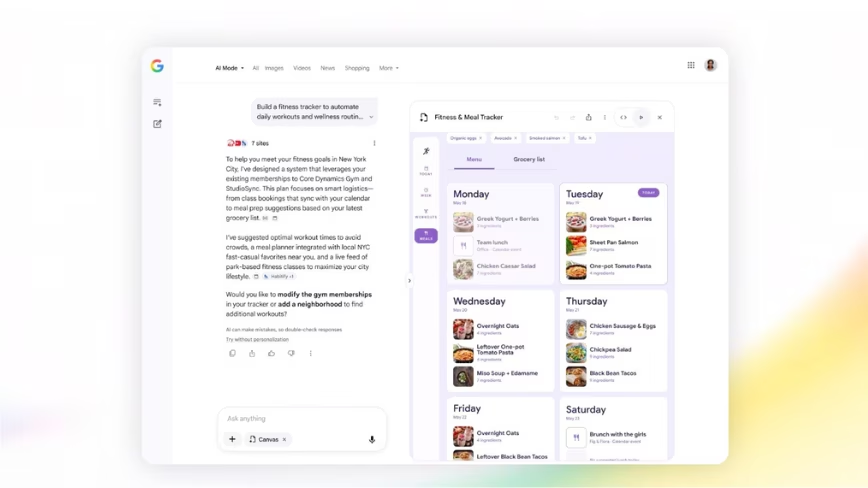
One such feature was ‘Face Unlock’, a face-recognition software feature confirmed by Google’s Andy Rubin to have been created by PittPatt – a Pittsburgh-based company that was acquired by Google earlier this year. The company was responsible for the development of the new security feature, which intelligently matches specific parts of the handset owner’s face to unlock their handset without so much as a button or screen press.
As soon as Google’s new Face Unlock feature was announced, many were quick to pounce on the new feature to suggest that the security feature could be bypassed simply by presenting a locked Android handset with a photo of the phone’s owner.
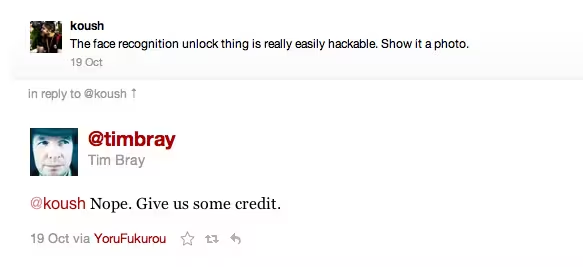
That was the exact thing that Koushik Dutta (Koush), the lead developer of popular Android aftermarket firmware CyanogenMod, remarked, stating in a tweet that “the face recognition unlock thing is really easily hackable. Show it a photo.”
The tweet was obviously seen by the powers that be at Google, including Android-focused Developer Advocate Tim Bray, who was quick to point out that it was not the case, and that people should give the search giant some credit:
It was safe to assume that Google wouldn’t let its face-recognition technology be bypassed using a photo but this confirms it. Good news for those who were worried about their friends hacking their smartphone by using a Facebook profile photo or something similar.
Get the TNW newsletter
Get the most important tech news in your inbox each week.