NC State University researchers have discovered an SMS phishing (smishing) vulnerability in the Android Open Source Project (AOSP) and thus is present in almost all Android versions, including Donut (1.6), Éclair (2.1), Froyo (2.2), Gingerbread (2.3), Ice Cream Sandwich (4.0), and Jelly Bean (4.1). They have tested the flaw on multiple popular Android devices, including the Google Galaxy Nexus, the Google Nexus S, the HTC One X, the HTC Inspire, the Xiaomi MI-One, and the Samsung Galaxy S3.
A video of the researchers exploiting the security hole in the last one was uploaded on YouTube just yesterday, catching our eye:
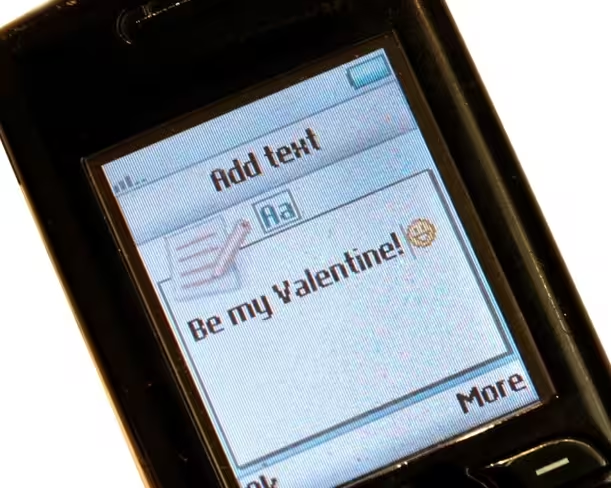
As you can see, smishing is a social engineering technique that uses cell phone text messages to bait victims into divulging their personal information, such as passwords for user accounts. The hook is usually a Web site URL in the text message, or a phone number that connects to an automated voice response system.
This particular vulnerability allows for smishing since an Android app can fake arbitrary text messages, making it appear that the user has received an SMS from someone on the phone’s contact list or say, from a trusted bank. The good news is that the researchers immediately contacted Google about the flaw, and the company responded promptly and positively:
We notified the Google Android Security Team on 10/30/2012 and were — as always — impressed to receive their response within 10 minutes. The confirmation of the vulnerability presence arrived on 11/1/2012 — two days after our initial report. From their response, we can infer that they took this issue seriously and investigated it without delay.
The vulnerability is now confirmed and we [were] told that a change will be included in a future Android release. We are not aware of any active exploitation of this issue.
The last part is also crucial: the researchers are unaware of the flaw being exploited in the wild. Since they responsibly disclosed the vulnerability to Google, it will hopefully be fixed before malicious parties can take advantage.
The group promises not to publish the details of the vulnerability until a final fix is out. In the meantime, you can protect yourself in two ways. The first is being cautious when downloading and installing apps (particularly from unknown sources) and the second is paying close attention to received text messages to try avoid being duped by possible phishing attacks.
It’s not clear how quickly and effectively Google will be able to deliver a patch to its users. Given how slow Android users are in adopting new versions, for various reasons that are rarely their fault, this issue may end up causing problems for months if not years to come.
See also – Android grabs 75.0% market share in Q3, followed by 14.9% for iOS and 4.3% for BlackBerry and FUD alert: 72% of all Android apps on Google Play access permissions they shouldn’t
Image credit: Jenny Rollo
Get the TNW newsletter
Get the most important tech news in your inbox each week.