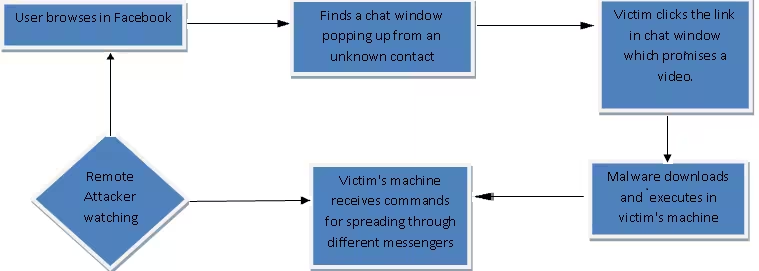
A newly discovered botnet is adding victims to its list by claiming to be an interesting video from a Facebook user. That’s nothing new. Here’s what makes this malware unique: it can spread via multiple instant messaging services, including Facebook Chat, Skype, Google Talk, Pidgin, Windows Live Messenger, Yahoo Messenger, and even ICQ.
The initial point of contact is Facebook (not surprising given that it’s the world’s most popular social network): the malware’s filename is typically something like “Picturexx.JPG_www.facebook.com.” It proliferates through the social network via an Ajax command that makes it look like the message came from one of your Facebook friends.
Once the malware is on the machine, it can receive commands from a remote attacker. From there, the victim’s computer sends out instant messages via the aforementioned platforms in a constant attempt to infect more PCs, according to McAfee:
Once on your machine, the malware bypasses the Windows Firewall by using the command line “netsh firewall allowed program” or by modifying the firewall policy to add itself as an allowed program. It then adds itself to start up when you reboot your computer and copies itself to another folder for safe keeping, marking the copy as a hidden file with read-only attributes. If you are checking for an infection, here are the three paths it might be in: the Windows folder, the Program Files folder, or the Public folder.
The malware does a series of checks for anything that can get in its way, and then disables them: antivirus software, Windows Update, and even Yahoo update software. It even changes the Internet Explorer start page, and modifies Chrome and Firefox’s preference files.
As a general word of caution, don’t click on any links you are sent via instant message. If you really can’t help yourself, always message your friend to make sure they really did send you something.
Image credit: stock.xchng
See also: Facebook tries to stop spam from flooding its help forum, fails
Get the TNW newsletter
Get the most important tech news in your inbox each week.