Mozilla on Friday announced it has added Java 7 Update 9, Java 7 Update 10, Java 6 Update 37, and Java 6 Update 38 to its Firefox add-on block list, following yesterday’s news of a new vulnerability. The critical security hole, which allows attackers to execute malicious software on a victim’s machine, is currently being exploited in the wild and is also available in common exploit kits.
Since there is no patch available from Oracle, Mozilla decided to act by taking precautionary steps to protect its users. Older Java versions are already blocklisted due to other vulnerabilities, and with today’s additions, all Firefox users are protected by either existing plugin blocking or Click To Play defenses.
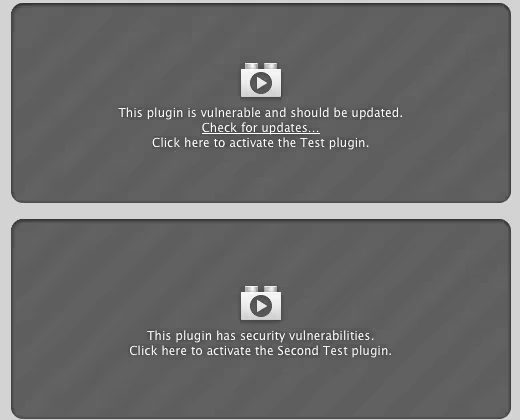
The former is straightforward, but here is how the latter, which applies to today’s block, works:
The Click To Play feature ensures that the Java plugin will not load unless a user specifically clicks to enable the plugin. This protects users against drive-by exploitation, one of the most common exploit techniques used to compromise vulnerable users. Click To Play also allows users to enable the Java plugin on a per-site basis if they absolutely need the Java plugin for the site.
This feature is available as of Firefox 17. It looks like this:
The prompt tells you that the plugin is vulnerable and thus Firefox has stopped it from loading automatically. If there is an update available, you will be prompted to update the plugin, but in this case that won’t happen till Oracle issues Java 7 Update 11 and Java 6 Update 39.
When that happens, we’ll let you know. Until then, we recommend uninstalling Java if you don’t need it and disabling it if you do.
See also – Oracle’s Java vulnerability left open since October 2012 ‘fix’, now being used to push ransomware and New Java vulnerability is being exploited in the wild, disabling Java is currently your only option
Image credit: Flavio Takemoto
Get the TNW newsletter
Get the most important tech news in your inbox each week.