Alexei Borodin, the same hacker who came up with the recent in-app purchase exploit that allowed free transactions for iOS users has struck again with a new method that allows users of Mac apps to do the same. The ‘In-Appstore for OS X’ service uses a method that’s very similar to that used on iOS devices to spoof transactions made to Apple’s servers.
We won’t rehash the method too much here, as we covered it in-depth with our previous article. The way that users implement it is slightly different on OS X than it is on iOS, but the root method is basically similar.
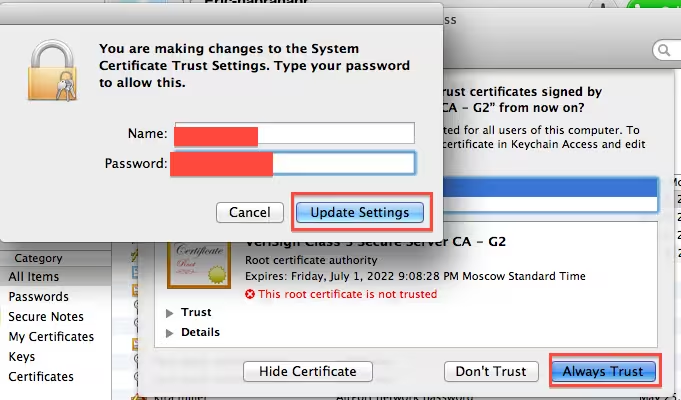
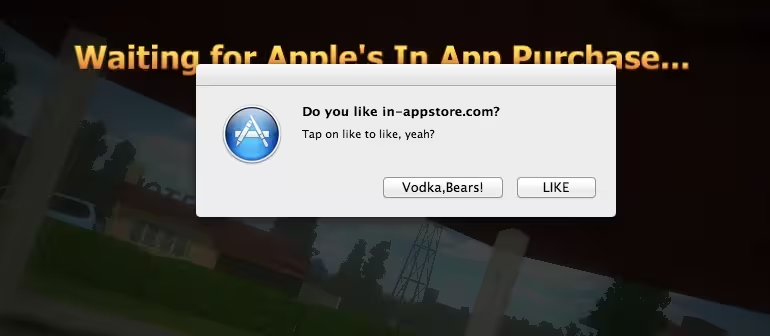
After installing two local certificates, a user points their computer’s DNS settings at Borodin’s server and it pretends to be the Mac App Store, issuing verification of the purchase. It’s not incredibly simple, but it’s not all that hard either. This time there is a companion app called ‘Grim Receiper that must be run on the local machine to facilitate the process as well.
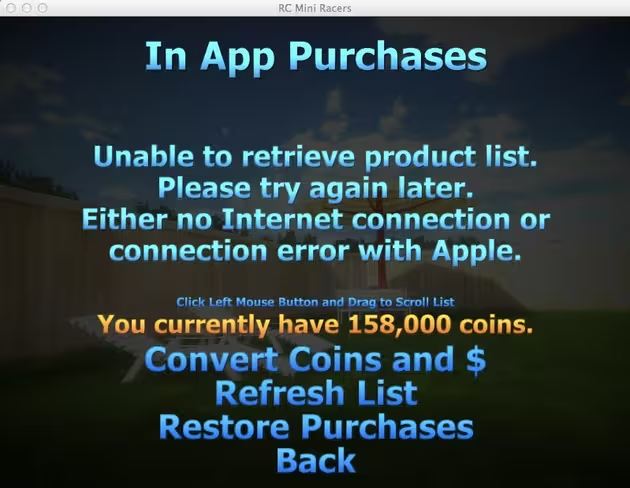
It effectively bypasses the simple receipt system that Apple has in place for developers,which has allowed over 8,460,017 free purchase transactions, according to stats provided by the hacker.
Earlier today, Apple introduced a method for iOS developers that would allow them to encrypt and verify their digital receipts with Apple, using two previously private APIs. It’s not clear whether Apple would be able to implement a similar temporary fix, or whether it would take more effort. If the methods are similar, however, the fix should be easy as well.
In-app purchasing is much more common in iOS apps than it is in Mac App Store apps, but any of this kind of theft is bad for the ecosystem and bad for developers. Here’s hoping that Apple enacts a swift fix on OS X as well as iOS.
The upcoming version of OS X, 10.8 Mountain Lion, is set to be released later this month some time. This could give Apple enough time to tackle a fix for the problem, though any true correction would likely have to take place on the developer’s end as well.
Get the TNW newsletter
Get the most important tech news in your inbox each week.