Cybersecurity researchers have always had an unspoken truce with companies. When hackers find a problem, they typically report it to the company and give them a chance to fix it before going public with it. This often leads to ‘bounties’ the company pays out for spotting the vulnerability, although not always.
A cybersecurity firm called MedSec just found a new way to monetize its research — Wall Street.
MedSec is foregoing the traditional approach by selling information directly to a short-seller called Muddy Waters Research. The investment firm then places bets in the form of a short-sale — a wager that the company will decrease in value — on Wall Street before making the information public. Once information of security vulnerabilities hits the airwaves, it often leads to a decrease in a company’s stock price, thus netting Muddy Waters Research a tidy profit. A portion of this profit is then paid to MedSec.

The deal represents a changing of the guard as cybersecurity firms look for additional ways to monetize. The potentially lucrative new strategy leaves ethical questions, but is currently legal — although it resides very much in the gray area.
MedSec’s new strategy became public after news broke that it bypassed St. Jude Medical and went straight to Muddy Waters Research after finding vulnerabilities in the company’s implantable heart equipment.
According to MedSec chief executive Justine Bone:
“We felt that if we were to take a traditional course and engage directly with [St. Jude Medical] — as others had done before — it was highly likely or almost certain that we would get hushed up and it would be brushed aside,” she said, citing a 2014 Reuters report about the Department of Homeland Security investigating security flaws in St. Jude’s products.
MedSec demonstrated vulnerabilities in pacemakers that could lead to hackers speeding them to dangerously fast rates, or quickly draining the devices’ batteries.
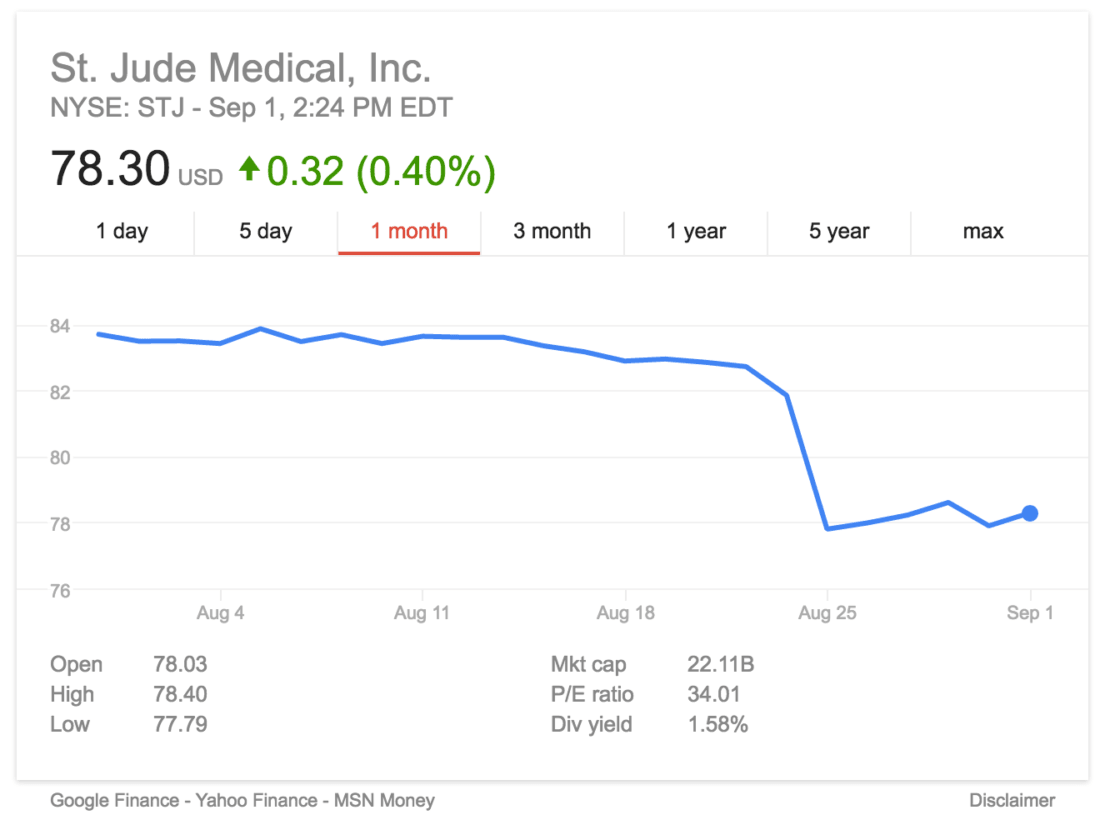
Once the news broke, the stock plummeted eight percent and Muddy Waters Research profited.
St. Jude denies the allegations that its implantable heart equipment is vulnerable, calling the report “false and misleading” before questioning the methodology behind the findings. St. Jude Medical also reported working with “third-party experts, researchers, government agencies and regulators in cybersecurity” to protect its devices.
Muddy Waters countered St. Jude’s claims with a new report and video evidence that demonstrates the attack.
Tuesday, however, researchers at the University of Michigan found MedSec’s research inconclusive.
While the two fight over the findings, St. Jude’s stock still hasn’t recovered to its previous levels from before the story broke. Depending on when Muddy Waters Research sold the shares, it could still be profiting over the back-and-forth between the two companies.
Regardless of who’s correct, Muddy Waters presumably profited from news of a vulnerability that normally would only see a payout to the security firm through a bug bounty program. This signifies a potential shift that could see other cybersecurity firms — and investment firms — attempting the same sort of arrangement.
Welcome to 2016.
Get the TNW newsletter
Get the most important tech news in your inbox each week.