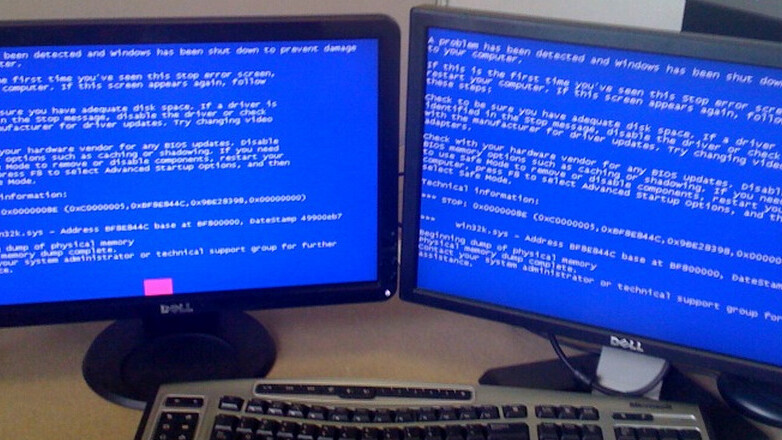
 Today Microsoft released August’s Patch Tuesday set of updates, which contained 13 total bulletins.
Today Microsoft released August’s Patch Tuesday set of updates, which contained 13 total bulletins.
Two of the thirteen bulletins were marked as ‘critical,’ nine deemed ‘important,’ and two were marked as merely ‘moderate’ in importance. The two critical bulletins involve Internet Explorer and Windows. What follows is Microsoft’s full explanation of the two worst vulnerabilities:
Cumulative Security Update for Internet Explorer (2559049)
This security update resolves five privately reported vulnerabilities and two publicly disclosed vulnerabilities in Internet Explorer. The most severe vulnerabilities could allow remote code execution if a user views a specially crafted Web page using Internet Explorer. An attacker who successfully exploited any of these vulnerabilities could gain the same user rights as the local user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
Vulnerabilities in DNS Server Could Allow Remote Code Execution (2562485)
This security update resolves two privately reported vulnerabilities in Windows DNS server. The more severe of these vulnerabilities could allow remote code execution if an attacker registers a domain, creates an NAPTR DNS resource record, and then sends a specially crafted NAPTR query to the target DNS server. Servers that do not have the DNS role enabled are not at risk.
This month’s patches are relatively numerous in number when compared to July, which contained only four bulletins. Still, no month in recent memory can top April’s massive 64 bulletins. May’s patch release contained a mere two bulletins.
As TheRegister notes, Microsoft seems to be in a cycle of releasing a large set of patches one month, followed by a smaller set the following month. The company could be doing so to ensure that it only deals with bad patch press every other month, but it is far more likely that this is simply the rate of the discovery of new vulnerabilities.
You can find all the information on the release here.
Get the TNW newsletter
Get the most important tech news in your inbox each week.