Just this morning Motherboard exposed one of the largest attacks yet, a massive breach of private user data from tech toy manufacturer VTech.
The hack exposed nearly 5 million parents as well as the names, genders and birthday information of more than 200,000 kids. What’s worse, the kids’ data is easily matched to that of the parents which would make it relatively easy to find their home addresses.
During his attempt to verify the leak, the journalist that originally penned the story, Lorenzo Franceschi-Bicchierai, reached out to Microsoft MVP for Developer Security, Troy Hunt.
It’s from Hunt’s analysis that we see just what went wrong.
Hunt’s first step was to verify the data. He did this through his own service, ‘Have I been pwned?’ (HIBP). HIBP is a free opt-in service that attempts to notify users if their accounts have been compromised in a data breach.
In 24 hours, he received six responses that seemed to back up the validity of the unnamed hackers claim.
From there he went about seeing just how severe the leak was.
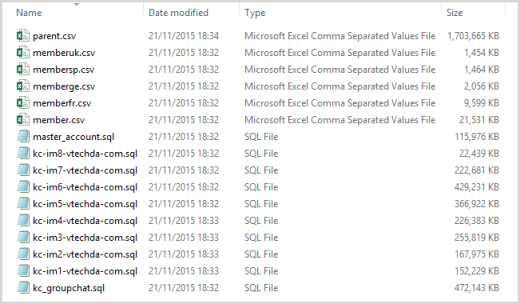
The image above shows the files originally provided to Franceschi-Bicchierai.
Right at the top, Hunter spotted the “parent.csv” file and opened it to take a closer look at the spreadsheet.
Inside the “parent.csv” spreadsheet Hunter found 4,862,625 rows and the column headings that contained name, email, password question and hint, secret answers, IP and address information.
Hunt then discovered the passwords were indeed encrypted, albeit weakly. The encryption was just a straight MD5 hash — a weak algorithm crackable in just minutes.
If this weren’t bad enough, the ease at which you can link a kid back to a parent (complete with home address) is truly frightening.
This is a self-referencing table, that is it has keys that refer back to itself. What it then means is that you get one record like this for the parent including their email address with an encoded @ symbol:
215836, 'foo%40bar.com', 'kc-im2.vtechda.com', 0, 2700413, 2700413, 'USeng', '2013-12-25 13:55:21', NULLAnd then a child record which references it like so:
215841, 'LittleJohnny', 'kc-im2.vtechda.com', 3974296, 0, 2700413, 'USeng', '2013-12-25 13:55:23', NULLYou can see how the parent_id of the child – 2700413 – relates back to the ID of the parent. This is not just a relational parent / child structure, it’s a literal real world biological implementation of that. The parent’s record can then be pulled from the parent CSV file I mentioned earlier on and contains all the values such as address, password and security questions.
Using the registration_url column, Hunt was able to source the information back to the site used to register it. The following URLs were affected:
- www.planetvtech.com
- www.lumibeauxreves.com
- www.planetvtech.fr
- www.vsmilelink.com
- www.planetvtech.de
- www.planetvtech.co.uk
- www.planetvtech.es
- www.proyectorvtech.es
- www.sleepybearlullabytime.com
- de.vsmilelink.com
- fr.vsmilelink.com
- uk.vsmilelink.com
- es.vsmilelink.com
What VTech did wrong
The major failing in the way VTech handled customer data was through unencrypted, non-SSL delivery of communication. Login, passwords, addresses and the like were all delivered over a standard HTTP protocol with no protection for users.
Once the information hit the database, VTech failed again.
The kids’ passwords were stored in plaintext and the adult passwords used weak encryption. It’s not the way large corporations encrypt data, and it doesn’t protect anyone but those who used incredibly secure passwords. We know that most don’t.
Possibly the most frustrating part of the leak was in the way VTech handled it.
“On November 14 [Hong Kong Time] an unauthorized party accessed VTech customer data on our Learning Lodge app store customer database,” Grace Pang, a VTech spokesperson, told Motherboard. “We were not aware of this unauthorized access until you alerted us.”
Thing is Motherboard had notified VTech of the breach days before the incident.
Worse, when VTech announced the breach publicly, today, it completely glossed over just how severe it was. The press release doesn’t mention the total number of people affected, the poor encryption used on passwords or that the breach exposed identifying information about children.
VTech basically delivered a free class on exactly what not to do when handling sensitive customer information, tip-toed around the edges of what actually happened and will now have to face the music for its ineptitude at dealing with the situation both pre- and post-hack.
Luckily, the hacker doesn’t seem to have any malicious plans. When asked by Motherboard what he intended to do with the data, he replied, “nothing.”
➤ One of the Largest Hacks Yet Exposes Data on Hundreds of Thousands of Kids [Motherboard]
Get the TNW newsletter
Get the most important tech news in your inbox each week.