
If you own or know somebody that has an iPhone, the chances are you will have heard of the phrase “Jailbreaking”. Put simply, jailbreaking is a process used to remove restrictions within Apple’s iOS software, providing opportunities for casual smartphone users and developers to perform functions and run apps outside of Apple’s walled garden.
Apple released the original iPhone in June 2007, the first jailbreak method (which was originally used to enable custom ringtones) came under two weeks later. Over the next year, a number of different developers and hackers were able to find keys to the system disk on Apple devices, opening up the iPhone and iPod Touch, until the Jailbreaking scene saw its first dedicated team create a tool that allowed iDevice owners to remove restrictions on their smartphone via a simple graphical user interface.
The iPhone Dev Team released the tool, named PwnageTool, signifying the start of a collective that worked on opening up what Apple would patch with each new release of its iOS software, giving birth to the Jailbreak scene. With Apple battling to restrict what its users could do on their devices, protecting both developers and operators from app misuse or intensive bandwidth hogging, it became – and still is – a race to exploit the in-built protection within Apple’s core frameworks, providing notoriety in the community and now a huge amount of consumer and media interest.
Over the past 4 years, the Jailbreak scene has seen a number of developers join the community and start their own iOS hacking groups, the most notable including; MuscleNerd, PlanetBeing, Geohotz, Comex, p0sixninja, chronic, DHowett, jan0, Jaywalker, OPK, posixninja, semaphore, westbaer. Some belong to the iPhone Dev Team, others to the Chronic Dev Team, but the goal remains the same – to exploit Apple’s software and hardware to remove restrictions from the iPhone, iPod and iPad.
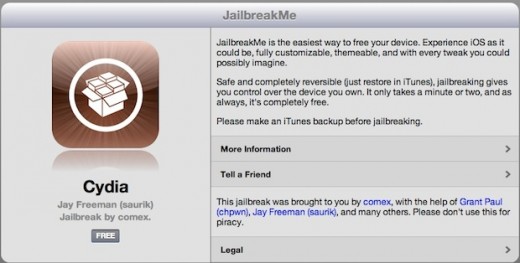
We’ve seen ultrasn0w, greenpois0n, JailbreakMe, redsn0w and many other tools to complete the process, making it easy for the casual user to remove barriers embedded on their devices.
The Jailbreaking Scene As It Stands Now
Key figures working on iOS exploits have not only gaining notoriety amongst the Jailbreak community and become well-known by iOS device owners, they have also attracted attention from Apple and others technology companies.
Comex, real name Nicholas Allegra, is perhaps the most well-known figure on the Jailbreaking scene, thanks largely to his work on the JailbreakMe exploit which could jailbreak an iOS device simply by visiting a website. Comex set up a specially crafted PDF file, that when loaded, would be able escalate privileges on a user’s smartphone or tablet and open it up to the installation of Cydia, a third-party application and modification ecosystem that exists as the Jailbreakers store of choice.
With Apple’s iOS 4.3.3 firmware vulnerable to a simple website visit, the company must have recognised comex’s talent because they went and made him an intern at 1 Infinite Loop. Yes, the company went and hired the guy that was causing them so many headaches – resulting in comex declaring he would not continue his work within the jailbreaking scene (which many see as a win for Apple).
The company may have also gotten its claws into MuscleNerd, unofficial spokesman of the iPhone Dev Team, after it was revealed that he had taken a tour of Apple’s offices. It is not known if he will take a position at Apple but the very public nature of the visit suggests there is more to just a tour of the Cupertino campus.
Geohot, infamous iPhone and PlayStation 3 hacker, is now working for Facebook.
Jailbreaking is so widespread, the scene has its own convention, called JailbreakCon (MyGreatFest until this Saturday), from which we were able to speak to some of the most prominent members of the community.
The iPhone 5 and iOS 5
With Apple expected to launch a next-generation iPhone in the coming weeks, focus has switched to a device that many believe will be called ‘iPhone 5’ and Apple’s new iOS 5 software, which introduces a number of significant new features and the launch of cloud-based services by the company.
With the launch of the iPhone 5, the Jailbreak community will instantly turn to the iPhone Dev Team and Chronic Dev Team for a solution to open their devices. Both groups are working on a way to do this, but with Apple’s engineers working hard to further protect users and developers with each new release of the iOS software, both teams are having to resort to more complex and innovative ways to bypass protective measures has put in place.
At MyGreatFest (now JailbreakCon), two Chronic Dev Team members, OPK and p0sixninja, took to the stage to present a brief history on their jailbreaking journey as members of the Chronic Dev Team and, most importantly for attendees, deliver a progress update on the state of a dedicated iOS 5 (and iPhone 5) jailbreak.
The good news for iDevice owners is that the Chronic Dev Team has made progress on its iPhone 5 jailbreak, with posixninja telling attendees:
The team is as ready as it can be for the iPhone 5 jailbreak, without having the actual handset. Once the iPhone 5 is available, the Chronic Dev Team will be working hard to find a jailbreak solution, and release it to the public.
The jailbreak solution will be a “Userland” exploit, a way of jailbreaking the device by modifying commands that exist outside of the iOS kernel. Tools like JailbreakMe exist as Userland exploits, patching iDevices at a software level to actually Jailbreak them but not provide low level control, something that a boot exploit can deliver.
The only downside of a Userland exploit is that they are extremely easy to patch, something that Apple has become more and more prompt with. With Apple’s iOS 5 firmware still in beta, a release will only be made available when the software has been made available to the public.
Posixninja says that the iPhone 5 jailbreak will incorporate five exploits to gain control over the smartphone:
“It uses a bunch of different layers, five exploits one after the other which will be chained together to affect the kernel. As a result the jailbreak will not be web-based, it will be similar to the Spirit jailbreak.”
The Chronic Dev Team duo announced that the group now exists as a corporate entity, although it is a non-profit company. All members of the team now belong to Chronic Dev LLC, which p0sixninja said will work on finding and training “the next comex”, turning that person “into a hacking machine”.
As a result, the group/company is looking for funding and is said to be making progress.
Behind the scenes, all of Chronic’s members communicate primarily via IRC, using the real-time protocol to work together despite the fact that its members are spread across the globe. Posixninja says that decisions or progress can sometimes be slow due to the fact that some members reside in countries like Australia and others in the U.S, but have also utilised a CRM tool to help collate code, discussion and ideas.
Each member of the Chronic Dev Team works on specific features when releasing a successful Jailbreak exploit:
“We have members that work on the exploits, some that work on reverse-engineering, others concentrating on Objective C – all of which come together to release the exploit on different platforms. We focus on cross-platform releases from the start, releasing a tool for Mac and then trying to port it to Windows just doesn’t work.”
With an obvious race between the iPhone Dev Team and the Chronic Dev Team, OPK briefly noted Chronic’s relationship with its so-called “rivals”:
“We have worked with the iPhone Dev Team, we communicate but primarily strive towards a common goal. Our code is original and we don’t borrow code, we certainly don’t take exploits from other teams. We are a research company.
We have code we don’t want to share, they have code they don’t want to share.”
Fighting Apple
Apple doesn’t want its closed system opened, so it continues to introduce new ways to protect the iOS kernel and associated codebase.
Apple has tried to negate us a couple of times; it has moved debuggers, making it harder but not impossible to exploit. There have been times where we have been actively blocked.
One challenge was have found is the introduction of ASLR (Address Space Layout Randomization), where anything written to memory is random. Our exploits have to figure where everything is at, where it is located and put it all together and make it work.
Apple also uses DEP (Data Execution Prevention) makes it so data areas can’t contain code. Data is only read and write and only code areas are executable, so we have to write code that can find and use Apple’s own code against itself.
Apple implemented ASLR, a technique that randomizes memory addresses used to store key data, with the release of iOS 4.3. The new technique makes it difficult to exploit memory-related security vulnerabilities like buffer overflows, as the attacker can’t predict the addresses where the payload will be written.
Whilst ASLR makes it a lot hard for coders to exploit systems, it doesn’t make it impossible, in fact it was defeated by comex with the release of JailbreakMe 3.0. The company quickly patched the flaw in its next release.
To this day, the Chronic Dev Team has never been subject to legal action from Apple (which might be as a result of a U.S legal ruling legalising jailbreaking).
However, Apple engineers have been quick to note the progress of the Chronic Dev Team; posixninja remembers meeting an Apple engineer at a Microsoft party held at the popular hacking convention DefCon:
“We somehow managed to get into a Microsoft party and met an Apple employee. He was an Apple engineer and when he found out who we were, he told us ‘there are lots of bugs in places you aren’t looking’. Surprised, I replied ‘then why aren’t you fixing them?’.
He said that Apple management is pushing them so hard that as a result, Apple’s building environment is fractured, a lot of the time the left hand doesn’t know what the right hand is doing. Deadlines were so tight, the engineer told us if they patched some of the bugs, they would break something else – everything is subject to time constraints.”
Conclusion
Its a testament to the Jailbreak community that the Chronic Dev Team make up just a small part of the scene. Not only are there a number of prominent members helping to exploit the iOS filesystem, there is a complete ecosystem of apps, services and different tweaks for Jailbroken phones that help extend the feature-set of iOS devices, some proving lucrative for the developers that create them.
As Apple continues to boost its smartphone and tablet market share, the number of iPhone, iPod and iPad owners looking to Jailbreak their devices is only set to increase. This will increase the pressure on jailbreaking teams to perform their magic but it will also bring in a new stream of users who will willingly donate to keep the projects on course and provide time for various members to work out just how to crash an iOS device.
Next week, we will take a look at Cydia and the earning opportunities it creates. You hear stories of the huge amounts of money made via the App Store, you might be surprised just how much Jailbreak developers are making.
Big thanks to Chris Goguelin for providing photos of the event.
Get the TNW newsletter
Get the most important tech news in your inbox each week.






